How I got started and my journey in Cybersecurity
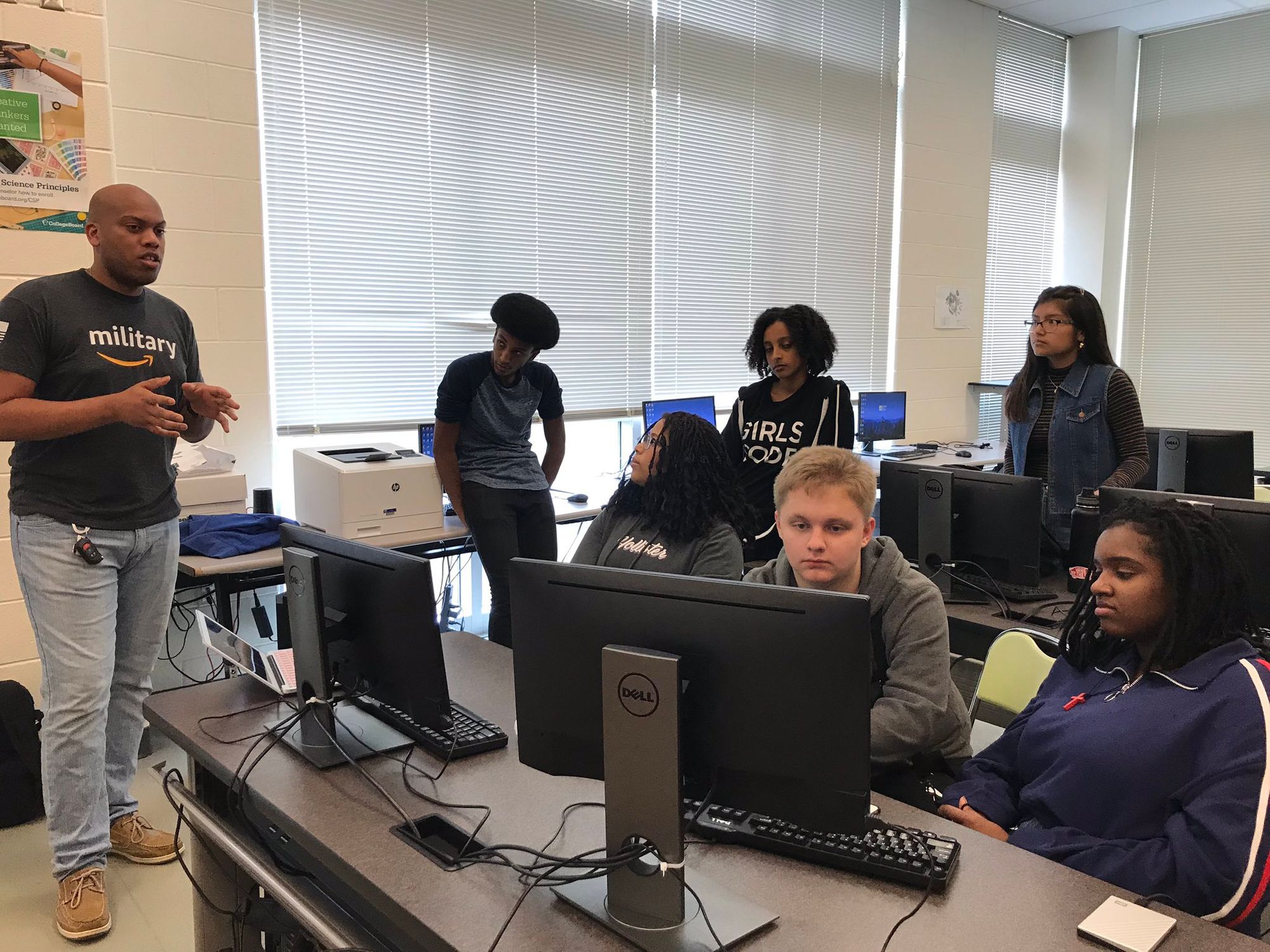
Recently I was extended an opportunity to speak at an undergraduate class of computer science. The topic I was to speak on was how I got into cybersecurity and my experience of different roles within the public and private sector of cybersecurity. I thought I'd share my story...


Recently I was extended an opportunity to speak at an undergraduate class of computer science. The topic I was to speak on was how I got into cybersecurity and my experience of different roles within the public and private sector of cybersecurity. I outlined what I would go over for the class so I thought I'd share my story here as well.
Who I Am
My name is Michael Banks and I am a practicing cybersecurity professional. I am currently a Security Engineer at Amazon Web Services (AWS) on the Security Operations Team. If you are not familiar, AWS offers an extensive array of reliable, scalable, and inexpensive cloud computing services. I am also a Signal Officer in the United States Army Reserve. I graduated from Augusta University (AU) in 2015 with a Bachelor of Science in Applied Information Systems & Technology with a Minor in Military Science. In December 2019, I graduated with a Master of Science in Information Security Management.
First off, I want to thank you for taking the time today and allowing me to share my experiences in the cybersecurity industry. Today I plan to go over how I discovered and got started in cybersecurity. I will go over the roles and experiences that I have had in the industry. Lastly, I will give you some tips that I believe will make you successful in the industry.
How I Started in Cybersecurity
I was always savvy and interested in technology and computers since my family got a Compaq Presario with Windows 95. I would play things like Carmen Sandiego, Math Blaster, and Reading Blaster. When I would go to one of my aunt’s houses, they happened to have Oregon Trail on 5 ½ floppies, and I enjoyed that game. Internet access wasn’t mainstream yet, so when I took a break from the games, I would tinker with other programs and play around with the command prompt to figure out what the commands did. I say all of this to say that when it was time to choose a major, I knew it would be something like Computer Science or Information Technology (IT). I knew I wanted to do something with computers, but I didn’t know what I wanted to do with computers. I always say to this day that I am willing to do anything but create video games. The game would never be completed because it would still be something I wanted to change or make look better.
During my junior year, I was in a Linux system administration class. You would hear all the time about events and different things related to computer science that offered extra credit, and I never missed one because if it’s free, it’s for me—and free class credit is something you don’t pass up. Not to mention, a lot of the events had free food. One opportunity that was shared was a BSides event. For those not aware, as stolen from their web page, “BSides is a community-driven framework for building events for and by information security community members. The goal is to expand the spectrum of conversation beyond the traditional confines of space and time. It creates opportunities for individuals to both present and participate in an intimate atmosphere that encourages collaboration. It is an intense event with discussions, demos, and interaction from participants. It is where conversations for the next-big-thing are happening.” The school was helping sponsor a BSides conference called BSides Augusta.

It was the second annual event hosted at our school. One of the graduation requirements was to complete either an internship or a senior capstone. Doing an internship was already on my mind that year. It just so happened that one of the speakers mentioned he was looking for interns. I went up to him after his talk and told him I was interested. The only thing he asked me was whether I could code. Luckily at the time I had experience with Java and C#, so I told him yes. It turned out he was the owner of a cybersecurity consulting firm and a former soldier and reverse engineer for the National Security Agency (NSA).
When I started my internship, I didn’t know what to expect, but I got to do some fantastic things like penetration tests for companies and organizations in both the public and private sectors. I sideloaded custom firmware on Wi-Fi routers that are still used today. I even got the opportunity to social-engineer my way into corporate and retail locations for companies I know you’ve heard of. That internship is how I discovered my love for cybersecurity.
Consulting Foundations

Fast-forwarding a bit, even though my internship as far as the school’s requirement for it was over, I continued to intern with that organization until I graduated. That work turned into my first job as an Information Security Consultant.
Consulting is a broad role, which is both a gift and a curse. What you do depends on the client and the case you’re given. I have worked on everything from penetration testing, ransomware recovery, and digital forensics to insider-threat cases, network buildouts, SIEM monitoring, phishing exercises, and even auditing. Often I hadn’t done the exact task before, but I was determined to figure it out, and when you have a good foundation in the fundamentals, everything in the computer world boils down to 1’s and 0’s.
Often you have to go to the client to do the work, so there was quite a bit of travel that came along with the job. I recall one year where I traveled 100 of the 365 days. Luckily for me, I love to travel, so it was amazing to see so many places. An average week at one point was flying out on Sunday afternoon, working from the client site all week, flying back home Friday, enjoying Saturday, and flying out the next day to do it all over again. On top of the technical work, the role required writing reports and documenting everything. So if you thought you were done writing papers after school, I’ll burst your bubble now—you will always be writing.
While being a consultant, one of the things unique to the organization that I was at was that they wanted you to do at least two public presentations a year. I think it was good publicity for the firm, but it was also a method to build up your communication skills, and with such a customer-facing role as a consultant, it was a way to get you comfortable with getting your name out there. I got to do some BSides conferences and speaking at some other conferences around the country. Another goal I set for myself was doing two industry certifications a year. So far, to this day, I have been able to continue that goal. I currently have about a dozen active industry certifications.
Building at AWS and Serving in Uniform
Security Engineer: My next opportunity came along in a pretty unexpected way. I always maintained a social presence, as mentioned before, with my previous job. One day a technical recruiter reached out to me on LinkedIn or “slid in my DM” as we say it nowadays. He mentioned a position for a Security Engineer in the D.C. Metro area in Northern Virginia. I expressed that I’d like to hear more about the job. I sent him my resume, and about five days had gone by and hadn’t heard from him; it turned out there was a typo on my resume for the email. THANKFULLY no one with that email didn’t take the job I was going for now. I gave the recruiter another email and got set up to do a couple of phone screens to test my technical knowledge. They flew me out—or “got me flewed out”—to their offices in Northern Virginia to test my technical knowledge again and see if I was the right fit for the company. About a week later, they sent me an offer to be a Security Engineer on the Security Operations team.
The AWS Security team is responsible for the security of all of the services offered by AWS. As a Security Engineer on the Security Operations team, I work cross-functionally to assess risk and help deliver countermeasures that protect customers and company data. I operate more in a leadership role in responding to security issues across the world’s largest cloud provider, which is pretty rewarding in an experience within itself to solve security problems at such a large scale.
My day-to-day job responsibilities include:
- Analyzing massive data sets to perform risk assessments
- Develop tooling and security controls to mitigate risks
- Support design reviews for developer tools to ensure that security objectives are met
- Work across teams at AWS to refine plans and obtain buy-in.
Army Officer: In parallel with my cybersecurity career, I’ve had a career in the United States Army Reserve. I enlisted back in 2011 at the beginning of my sophomore year in undergrad as a private first class. I did basic training or boot camp, along with some advanced individual training, and resumed school. I continued my Army Reserve experience with a Military Intelligence Unit in various roles until I graduated and commissioned as a Signal Officer in a Theater Tactical Signal Brigade. For those not aware of Signal, it’s the equivalent of the communications infrastructure that connect soldiers on the battlefield to one another and the Department of Defense Information Network (DODIN). I have recently moved to a Cyber Protection Team to do more cyber-related things for the Army Reserve.

Advice and Final Thoughts
I have had the unique opportunity to work at a private security firm out of college, a Fortune #2 public company, and serve in the federal government for almost ten years. If I can leave you with any advice on what I would want to know if I were starting my freshman year would be the following:
-
Get/Keep your writing game up! All organizations write reports, articles, documentation and you will never get out of it.
-
Learn in-depth and as much as you can around the fundamental principles of computer science. Everything from the networking protocols, how packets work, to the makeup of computers, assembly, and the operating systems like Mac, Windows, and Linux. All of the jobs, companies, and verticals that exist in the industry build on top of that. No matter what job you do or position you’re in, the more knowledge you have on the fundamentals will only propel you further because remember, at the end of the day in the computer world, it’s all just 1’s and 0’s.
-
Get as much experience as you can before you graduate, whether it’s personal projects, research, patents, work studies, or projects. I had my own virtualized lab by my junior year with an extra PC, but you can get experience by doing it yourself. Try to get internships because it’s a great way to have a job before you even start looking for one. It will set you apart from your peers that don’t have it, and organizations are looking for people with experience.
-
Network! Network! Network! Get your name out there. I am sure you all know that sometimes it’s not what you know but who you know will get you ahead in life. It’s how you get noticed and build relationships. Visit some conferences, start submitting talks to them. Keep a blog around the things you are doing. You never know who will be “sliding in your DM” offering a job.
Thank you for the opportunity to share my story. I hope this information helps, and I hope my experience gives you some idea of some of the options you have in the cybersecurity industry. I’ll be happy to take any questions you might have for me around anything in the cybersecurity realm or the military sphere. Also, feel free to connect with me on Twitter or Instagram at @4MikeBanks. Also, here’s my LinkedIn https://www.linkedin.com/in/mrmikebanks/.
Keep reading
View archiveWebsite and Blog Redesign
Today I’m launching a redesigned, integrated michaelbanks.org experience that brings my website and blog together into one platform.
Relaunching michaelbanks.org
Design goals, architecture decisions, and how I'm preparing the site for AI-assisted publishing.
The 5 Books Every Cybersecurity Professional Should Read
A group of industry professionals that I know started to talk about interesting books they've read and thus own our very own cyber book club began. Now I keep track of a running and ever-evolving list of books that I genuinely believe EVERYONE in the field and industry should...