5 Tips Airports Should Probably Pay Attention To
While being at the airport a lot, you tend to end up noticing some not so flattering things. In general, it's been my experience that all airports have issues.

One of the frequent realities of being an Information Security Consultant is traveling. Nine out of the ten times it is going to involve flying. When you spend that much time in airports, you start to notice some not-so-flattering things. In general, it's been my experience that all airlines and airports have issues. Delta is my personally preferred airline, so I tend to see their unflattering moments more than others. Learning is an important aspect of being a consultant, so let's walk through some of the things you may run into at the airport—and let’s make sure they don’t show up in any organization. All of them apply to any business with a network.
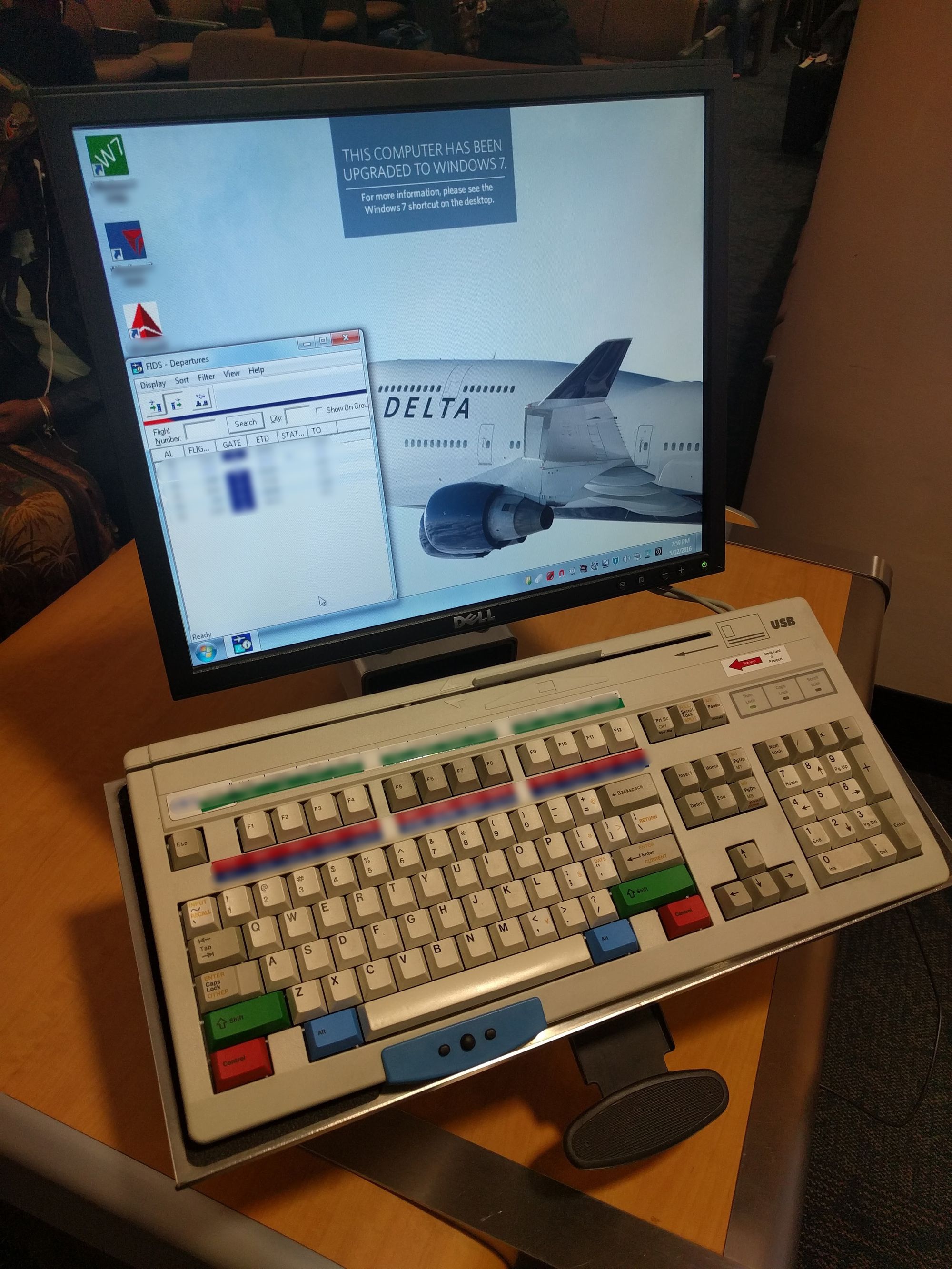
Recently, on my way home from an engagement, I was sitting in the waiting area for my flight and I noticed a kiosk right behind me. It didn't look like one of those kiosks that anyone could use. This brings us to our first tip.
Tip #1: Keep Non-Public Kiosks Out of Sight
Even if this is a public kiosk, you probably shouldn't place it in such a manner where anyone can see what a user is doing. I don't know about you, but I don't want everyone knowing my business. From a glance at the screen, it doesn't seem like a workstation for the public. With that in mind, let's assume this isn't public, and that brings us to another tip.
Tip #2: Always Lock Idle Workstations
In trusted or untrusted environments, there is nothing wrong with locking your workstation. I shouldn't even have to write anything to convince anyone that locking the workstation is a good idea, so I will leave it at that; even though you will probably run into it out there.
Tip #3: Don’t Advertise Your Shortcomings
We are halfway through 2016, and Windows 10 has been released for almost exactly a year now. I will concede to the fact that Windows 8 and Windows 8.1 were not such stellar incremental upgrades from an operating system standpoint, but for an airport or airline to be just now upgrading to Windows 7 makes me cringe. Could it be that they never changed the wallpaper, and they upgraded it years ago? I don't know, but I hope so. Either way, it shouldn't be advertised. A nefarious attacker, without getting on the network or scanning any boxes, now knows what operating system is in use and which exploits to focus on to gain a foothold.

Tip #4: Segment Everything
I don't know what the networking segmentation situation is of this system, how exposed it is, or what other sensitive systems it is connected to because:
- I'm not stupid enough to tamper with systems without authorization.
- I didn't want to touch something and cause damage, just in case the airport didn't segregate the system from other major systems needed for an airport/airline.
BUT! Someone can do a lot of homework on the network and configuration with a machine just sitting there. This system wasn't like this for only a couple of seconds—it sat vacant the entire time I was there waiting for my flight (~40 mins). Hopefully it's segmented, because that would be a nightmare if it was not. Also, please segment more than by just using a VLAN tag ID.
Tip #5: Nail the Basics First
All your security won't help if you don't even turn it on. Security is hard! Fixing and continually addressing the simple things—or the "low hanging fruit"—should be everyone's top priority. It is the first thing an attacker will try.
While this wasn't a formal assessment and more of an observation for the airport or airline in question, at Rendition InfoSec, where I work, we do assessments and would be happy to discuss opportunities to make your security better.
Keep reading
View archiveWebsite and Blog Redesign
Today I’m launching a redesigned, integrated michaelbanks.org experience that brings my website and blog together into one platform.
Relaunching michaelbanks.org
Design goals, architecture decisions, and how I'm preparing the site for AI-assisted publishing.
How I got started and my journey in Cybersecurity
Recently I was extended an opportunity to speak at an undergraduate class of computer science. The topic I was to speak on was how I got into cybersecurity and my experience of different roles within the public and private sector of cybersecurity. I thought I'd share my story...